Multi-factor authentication (MFA)
In Business, Official Blog, Tech-BLOG, Tech-Forum, TechnicalMulti-factor authentication(MFA)
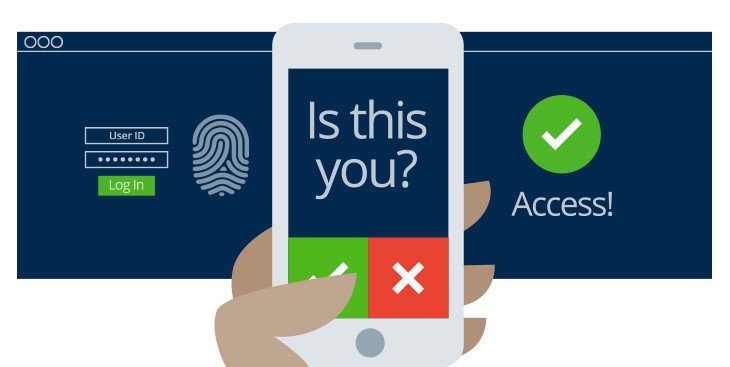
Multi-factor authentication is a method of computer access control in which user granted access only after successfully presenting several separate pieces of evidence for authentication mechanism- typically at least two of the following categories: knowledge(something they know), possession(something they have), and inherence(something they are).
Two-factor authentication
It is a combination of two different components.
Two-factor authentication is a type of multi-factor authentication.
A good example from everyday life is the withdrawing of money from an ATM; only the correct combination of the bank card (something that the user possesses) and a PIN (personal identification number, something that the user knows) allows the transaction to be carried out.
The authentication factors of a multi-factor authentication scheme may include:
- Some physical object in the possession of the user, such as a USB stick with a secret token, a bank card, a key, etc.
- Some secret known to the user, such as a password, PIN,TAN, etc.
- Some physical characteristic of the user (biometrics), such as a fingerprint, eye iris, voice, typing speed, pattern in key press intervals, etc.
Knowledge factors
Knowledge factors are the most commonly used form of authentication. In this form, the user is required to prove knowledge of a secret in order to authenticate.
A password is a secret word or string of characters that is used for user authentication. This is the most commonly used mechanism of authentication. Many multi-factor authentication techniques rely on password as one factor of authentication.Variations include both longer ones formed from multiple words (a passphrase) and the shorter, purely numeric ,personal identification number (PIN) commonly used for ATM?access. Traditionally, passwords are expected to be memorized.
Possession factors
Possession factors (“something only the user has”) have been used for authentication for centuries, in the form of a key to a lock. The basic principle is that the key embodies a secret which is shared between the lock and the key, and the same principle underlies possession factor authentication in computer systems. A security token is an example of a possession factor.
Disconnected tokens
Disconnected tokens have no connections to the client computer. They typically use a built-in screen to display the generated authentication data, which is manually typed in by the user.
Connected tokens
Connected tokens are devices that are physically connected to the computer to be used. Those devices transmit data automatically.There are a number of different types, including card readers, wireless tags and USB tokens.
Inherence factors
These are factors associated with the user, and are usually bio-metric methods, including fingerprint readers, retina scanners or voice recognition.